Cybersecurity
Securing the edge in a manufacturing facility
Manufacturers looking to gather more information at the edge need to have a strong cybersecurity program in place, but not enough do, leaving them at risk. See four ways to increase cybersecurity shields.
Top 5 Control Engineering content: August 22-28, 2022
The most-viewed content from the past week covered 5G, SCADA, programming, cybersecurity advice and more.
Nine reasons why ICS/OT infrastructure is insecure
Industrial control system (ICS)/operational technology (OT) infrastructure security is different in many ways from informational technology (IT) security. Nine reasons why the infrastructure is insecure are highlighted.
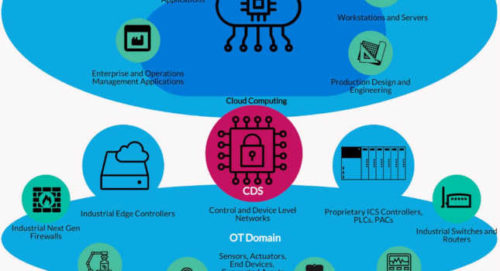
How cross-domain solutions can protect OT from IT-level attacks
Cross-domain solutions (CDS) can help secure communications between information technology (IT) and operational technology (OT) domains.
Assessing ransomware risk in IT and OT environments
Industrial organizations and governments are struggling to get their hands around the complicated cybersecurity issue of ransomware risk
Four cybersecurity technologies, concepts can reduce industrial network risk
Explore the qualities and benefits of zero trust, principle of least privilege and other methods of improving cybersecurity. Four key technologies and security concepts are highlighted.
Four cybersecurity approaches and strategies for industrial networks
Companies implementing a cybersecurity program need to have a clear agenda and know the tools available. Four approaches and products are highlighted.
What a shields-up approach means for industrial companies
As cyberattacks against manufacturers increase, companies are being advised to raise their shields and pivot toward a zero-trust cybersecurity strategy. Five zero trust elements are highlighted.
What’s behind the IT/OT divide?
The IT/OT divide comes from cultural differences, but the gap can be bridged by creating cross-functional teams, open communication and more.
Improving your OT cybersecurity posture
Companies need to ask fundamental questions about where they stand with OT cybersecurity in the short- and long-term to improve their position.